Community Safety & Public Alerts
Cybercrime Surge in Nigeria: How Digital Threats Are Targeting Citizens, Businesses, and Government Systems
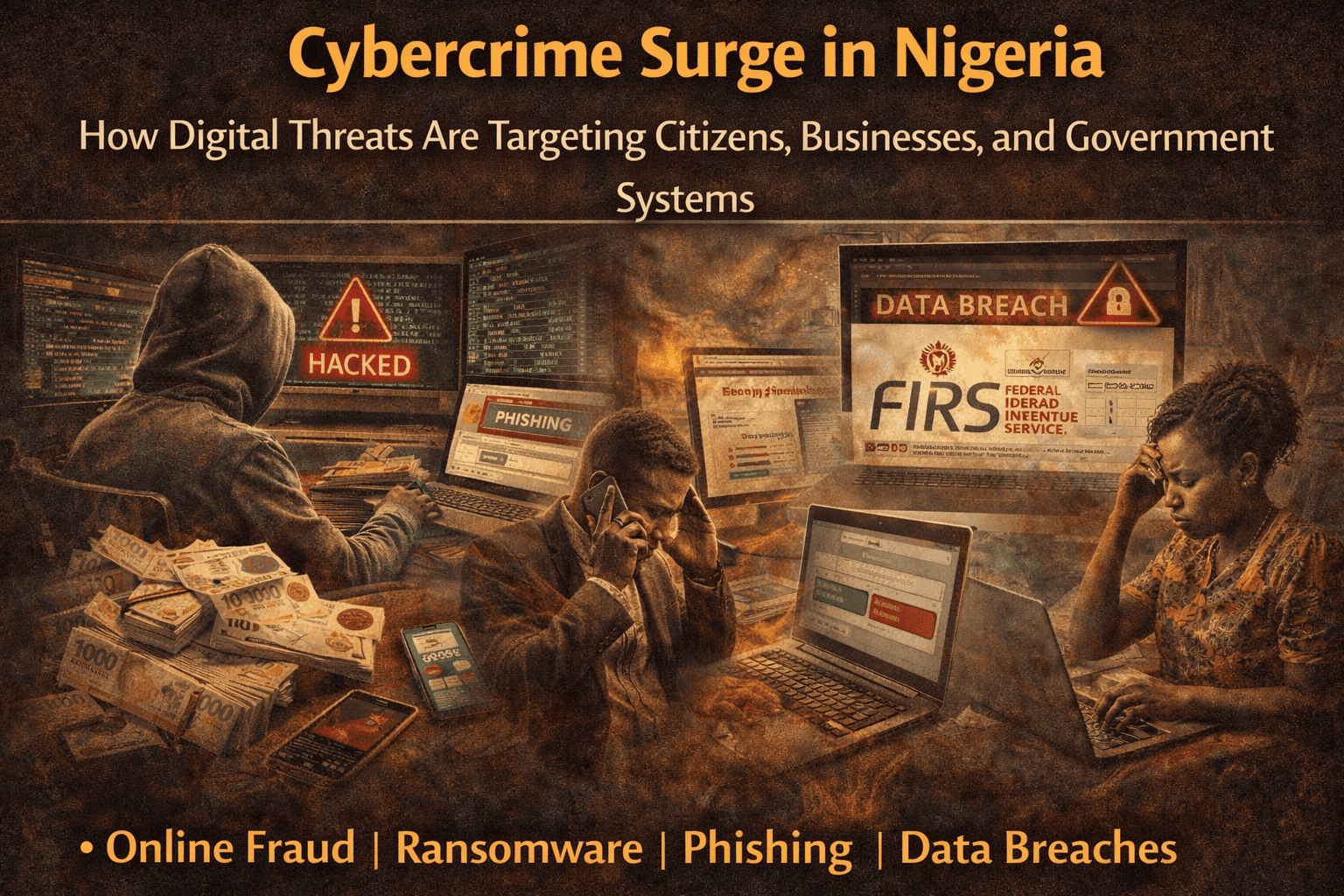
As Nigeria continues to grapple with physical insecurity, another form of threat is silently growing — cybercrime. From phishing scams and bank fraud to ransomware attacks and data breaches, the digital space has become a new frontier for criminals exploiting both private citizens and public institutions.
Security Brief Nigeria’s investigation shows that the rise in cybercrime is not just a technical issue — it has profound implications for national security, economic stability, and citizen trust in government digital services.
The Scope of the Cyber Threat
According to the National Cybersecurity Centre (NCC) and independent security analysts:
- Fraudulent online banking transactions have increased by over 30% in the past year.
- Ransomware attacks targeting government agencies have been reported in at least four states.
- Phishing schemes continue to exploit social media platforms and messaging apps.
- Identity theft cases surged, particularly involving e-payment platforms and online marketplaces.
A cybersecurity expert told Security Brief Nigeria:
“Criminals are now as sophisticated as some state actors. They can exploit vulnerabilities in government networks, trick ordinary users, and move funds across borders undetected.”
Common Cybercrime Tactics Observed in Nigeria
1. Phishing and Social Engineering
Attackers craft fake emails, SMS messages, and social media communications that appear official. Citizens are tricked into revealing passwords, OTPs, or personal information.
2. Mobile Money Fraud
The widespread use of mobile banking apps has created new vulnerabilities. Criminals use cloned SIM cards, fake USSD codes, and malware to access accounts.
3. Ransomware
Some cyber gangs have targeted critical institutions, encrypting data and demanding payment in cryptocurrency. Hospitals, local governments, and educational institutions are increasingly at risk.
4. Online Scams
From fake online shops to investment Ponzi schemes, Nigerians have lost millions to digital fraudsters. These scams exploit both fear and greed, often using social media as bait.
Why Cybercrime Is Growing Rapidly
Analysts attribute the surge in digital crime to several interrelated factors:
- Rapid Digitization – Nigeria’s push for e-governance and mobile payments increases attack surfaces.
- Low Cybersecurity Awareness – Many citizens are unaware of phishing tactics, malware risks, and safe password practices.
- Weak Legal Enforcement – Cybercrime laws exist, but enforcement is inconsistent, and prosecution remains low.
- Cross-Border Criminal Networks – Cyber gangs operate from abroad, using international anonymity to evade Nigerian authorities.
- Affordable Hacking Tools – Many cyber tools are available online at low cost, lowering the barrier to entry for aspiring cybercriminals.
Impact on Citizens, Businesses, and Government
Citizens
- Loss of personal funds through fraudulent transactions
- Identity theft and personal data misuse
- Erosion of trust in digital services
Businesses
- Financial losses and reputational damage
- Theft of intellectual property
- Operational disruption due to ransomware
Government
- Data breaches in public databases
- Reduced confidence in e-governance initiatives
- Potential national security implications if sensitive systems are targeted
Case Studies: Real Incidents in Nigeria
A. Lagos State Mobile Fraud
Over the past year, over 10,000 mobile banking fraud cases were reported. Many involved SIM card cloning and phishing SMS campaigns. Victims reported losing between ₦50,000 and ₦5 million per incident.
B. Kaduna State Education System Attack
Ransomware disrupted the administration of several secondary schools, encrypting student records and staff payroll data. Payment demands were made in Bitcoin, forcing schools to rely on backups and state intervention.
C. Federal Tax System Breach
Hackers infiltrated a state tax database, accessing taxpayer information. While financial theft was prevented, sensitive personal data was compromised.
Cybersecurity Measures and Government Response
The Nigerian government and private organizations are responding through:
- National Cybersecurity Strategy – Establishes guidelines for government, private sector, and citizens.
- Cybercrime Act Enforcement – Targets cybercriminals through legal prosecution, though enforcement remains a challenge.
- Public Awareness Campaigns – Educating citizens on phishing, malware, and online fraud.
- Collaboration with Tech Companies – Banks and mobile operators deploy anti-fraud tools and real-time monitoring systems.
- International Cooperation – Partnerships with INTERPOL, ECOWAS, and foreign cybersecurity agencies to tackle cross-border cybercrime.
Experts emphasize that while these measures are crucial, they must be continuous, adaptive, and widespread to match the evolving tactics of cybercriminals.
Expert Analysis
Cybersecurity specialists warn that Nigeria’s digital infrastructure is vulnerable because:
- Many systems use outdated software
- Encryption practices are inconsistent
- Digital literacy among citizens is low
- The enforcement of cybersecurity regulations is fragmented
Professor Chinedu Okoro, a cybersecurity expert, explains:
“Cybercrime is no longer just theft. It’s a national security threat. Criminals can disrupt government services, manipulate elections, steal state secrets, and even fund insurgent operations.”
Recommendations to Strengthen Cybersecurity
1. Strengthen Legal Frameworks
- Faster prosecution of cybercriminals
- Clearer regulations on data protection and breach reporting
2. Enhance Citizen Awareness
- Nationwide campaigns on password hygiene, phishing, and mobile app security
- Mandatory cybersecurity education for students and employees
3. Invest in Technology
- Modern firewalls, antivirus solutions, and intrusion detection systems
- Multi-factor authentication (MFA) for government systems
4. Establish Rapid Response Units
- State-level cybersecurity emergency teams
- Collaboration with banks and ISPs to quickly block threats
5. Encourage Private-Public Collaboration
- Shared threat intelligence between businesses and government
- Incentives for tech firms to provide cybersecurity solutions
Conclusion
As Nigeria continues to digitize, cybercrime will remain a persistent threat unless citizens, businesses, and government agencies work together. The surge in digital attacks is a wake-up call that security is no longer just physical — it is also virtual.
Building awareness, investing in technology, and enforcing laws are the only sustainable ways to protect the nation’s digital future. Citizens must remain vigilant, and authorities must act decisively to prevent Nigeria from becoming a global hotspot for cybercriminal activity.
Community Safety & Public Alerts
National Strategy to End Banditry Unveiled
Banditry Is Not Just Crime—It Is a War of Terrain, Economics, and Social Control
Banditry thrives where the state is absent or weak. It is sustained by several factors:
- Vast ungoverned forest belts offering natural cover and escape routes.
- Unemployment and rural poverty, which supply foot soldiers.
- Availability of small arms flowing from regional conflicts.
- Political actors who benefit from disorder or use bandits for influence.
- Limited enforcement capacity, especially in remote regions.
- Ethnic tensions and farmer–herder disputes exploited by armed groups.
Thus, fighting banditry cannot rely solely on military force. It must be:
- Political (leadership, coordination, accountability)
- Economic (jobs, infrastructure, local economies)
- Technological (surveillance, mapping, communication)
- Community-driven (information flow, trust networks)
- Judicial (prosecution, deterrence, correctional reform)
2. Banditry as a Networked Enterprise
Modern bandit groups operate like mobile criminal corporations:
- CEOs (warlords/leaders)
- Managers (mid-level commanders)
- Foot soldiers
- Informants
- Arms suppliers
- Negotiators
- Money-movers
- Political sponsors
- Local collaborators
A national strategy must break these layers one by one.
II. Components of a National Anti-Banditry Strategy
A successful roadmap must include five pillars:
- Security & Kinetic Operations
- State Presence & Governance Expansion
- Economic Transformation & Local Empowerment
- Justice, Rehabilitation & Deterrence
- Technology, Intelligence & Data-Driven Decision Making
Let’s break these down.
III. Pillar 1: Security & Kinetic Operations (Immediate Response Phase)
This is the most visible component but cannot stand alone. It must be reorganized into a coordinated national doctrine.
1. Establish Unified National Anti-Banditry Command
Instead of scattered efforts by the military, police, DSS, NSCDC, immigration, and forest guards, a nation needs a single command architecture to:
- centralize intelligence
- unify operations
- avoid duplication
- synchronize response
- monitor progress and failures
All commands in affected states would report to this central body.
2. Persistent Air-Ground Dominance
Air superiority is key because bandit enclaves are:
- deep inside forests
- accessible only by rough, narrow routes
- often surrounded by natural defensive terrain
A proper strategy includes:
- Armed drone patrols
- Night-vision helicopter surveillance
- Radar mapping of camps
- Heat-sensor tracking to detect mass movement
- Smart bombing—precise, not random
3. Forest Control Doctrine
Forest belts in Zamfara, Katsina, Niger, Kaduna, Benue, Taraba, Plateau, and Kebbi hold large enclaves. The state must develop a Forest Security Doctrine:
- Mandatory registration for all forest users
- UAV surveillance maps
- Buffer zones
- Ranger outposts every 30–50 km
- Forest access control (barriers, checkpoints, monitored entry points)
4. Strike, Hold, Build Strategy
The national strategy should use a 3-phase military stabilization model:
Phase 1 — Strike
- Attack camps
- Destroy logistics
- Neutralize commanders
- Block escape routes
Phase 2 — Hold
- Deploy police & forest guards
- Establish mobile bases
- Rebuild patrol roads
- Deploy technology for monitoring
Phase 3 — Build
- Restore governance
- Provide livelihood programs
- Rebuild schools and clinics
- Integrate communities into secure frameworks
5. Special Forces for Hostage Rescue
Kidnapping is a primary funding source. A nation must train:
- Dedicated hostage-rescue regiments
- Rapid response air-mobile teams
- Intelligence-led tracking squads
- Negotiation specialists
6. Border Security
Banditry is sustained by illegal arms movement. Strengthen border control with:
- biometric checkpoints
- terrain surveillance
- joint border patrols with neighboring countries
- cross-border intelligence fusion units
IV. Pillar 2: Expanding State Presence & Governance (Medium to Long-Term Phase)
Banditry grows where the state is missing, especially rural communities.
1. Government in Every Village
Each rural region needs:
- functional local government offices
- rural police posts
- ward-level intelligence cells
- mobile administrative teams
- rural courts
- social service officers
The absence of government equals the presence of bandits.
2. Rural Infrastructure Deployment
Build or rehabilitate:
- rural roads
- solar-powered lighting
- boreholes
- clinics
- schools
- micro-power grids
Banditry retreats where communities are economically alive and connected to the nation.
3. Community-Led Early Warning Systems
Train community structures to detect threats early:
- village security committees
- rapid reporting networks
- emergency communication lines
- safe alert centers
- whistleblower protection frameworks
This reduces surprise attacks.
V. Pillar 3: Economic Transformation & Local Empowerment (Root Cause Phase)
Banditry thrives on poverty, unemployment, and youth redundancy.
1. Rural Youth Empowerment
A national plan must create:
- farm-to-market hubs
- vocational training centers
- agricultural mechanization programs
- community mining cooperatives
- employment under rural infrastructure corps
Where young men have jobs, bandits lose recruits.
2. Regulated Grazing & Herding Reforms
Farmer–herder conflicts create breeding grounds for violence. Solutions:
- ranching transition incentives
- pastoralist integration programs
- cattle identification systems
- grazing route mapping
- livestock markets regulated for cashless transactions
3. Building Local Economies
Communities must have economic engines:
- cooperatives for farmers
- cottage industries
- food processing clusters
- rural logistics support hubs
A poor community is a captive community.
VI. Pillar 4: Justice System Reform & Deterrence
Bandits thrive because criminal justice is slow, weak, or compromised.
1. Fast-Track Rural Security Courts
Create mobile courts capable of:
- quick prosecution
- roadside hearings for minor offenses
- witness protection
- secure trial processes
Delays kill deterrence.
2. Modern Correctional Reform
Overcrowded prisons produce hardened criminals. Solutions:
- build high-security facilities
- separate petty offenders from violent criminals
- digital inmate management
3. Target the Money
Banditry is a business. Freeze:
- ransom accounts
- gold trade proceeds
- illegal mining revenue chains
- political sponsorship funding pipelines
When money stops, violence collapses.
VII. Pillar 5: Intelligence, Technology & Data Power
No nation can defeat banditry blindly.
1. National Banditry Intelligence Fusion Center
Centralize intelligence from:
- military
- police
- DSS
- forest rangers
- telecoms
- satellite imagery
- local informants
This enables real-time decision-making.
2. Telecom Data Tracking
Require telecom providers to enable:
- call pattern analysis
- geolocation of camps
- ransom communication intercepts
- mass-movement detection algorithms
3. National Forest Surveillance System
Use drones and satellites to:
- map camps
- detect night activities
- track movement from grazing paths
- identify heat signatures
4. Ransom Payment Monitoring
Cashless policy for rural areas must include:
- crypto surveillance
- mobile transfer monitoring
- suspicious account reporting
- blocked SIM protocols
VIII. Non-Kinetic Solutions: Hearts, Minds & Healing
Military force alone cannot win. Sustainable peace requires:
1. Dialogue with Non-Hardcore Groups
Some bandits are:
- misled youths
- people seeking survival
- displaced individuals
Reintegration programs may include:
- de-radicalization
- skill training
- farming grants
- supervised reintegration camps
- psychological counseling
2. Community Reconciliation
Conflicts between communities must be mediated via:
- truth and reconciliation panels
- inter-group peace treaties
- cultural-to-cultural dialogue
- joint farming agreements
- shared security structures
IX. Eliminating Enablers of Banditry
1. Political Sponsors
Banditry survives when politicians:
- shield criminals
- fund militias
- use violence for elections
A strict zero tolerance policy must include:
- asset forfeiture
- lifetime political bans
- high-treason classification
2. Illegal Mining
Many bandits finance operations through:
- gold mining
- lead and zinc extraction
- mineral smuggling
Government must:
- militarize illegal mining hotspots
- regulate artisanal mining
- deploy mining marshals
3. Traditional Structures Compromise
Compromised chiefs or district heads must be:
- prosecuted
- dismissed
- replaced through transparent procedures
X. National Communication Strategy
Public trust is a battlefield. Governments must control narratives.
1. Accurate, Verified Information Only
Briefings must:
- avoid panic
- avoid glorifying bandits
- avoid revealing operational secrets
- emphasize progress
2. Media Ethics Training
Journalists must be trained on:
- what to publish
- what not to publish
- operational security (OPSEC)
- national security reporting codes
3. Counter-Fake News Operations
Fake news feeds bandits. A nation needs:
- rapid debunking units
- digital monitoring teams
- prosecution for dangerous misinformation
XI. Community Partnership Strategy
Communities are the first line of defense.
1. Village Protection Units (Non-Armed)
Trained in:
- observation
- communication
- alert systems
- safe evacuation
- identifying suspicious activities
2. Women & Youth Engagement
These groups often:
- notice early changes
- detect unusual movements
- observe new strangers
Empower them with:
- reporting channels
- safe numbers
- community briefings
- security literacy programs
XII. Long-Term Stability Phase (10–20 Years)
Real security requires decades of sustained policy.
1. Education as Strategic Defense
To defeat future criminality:
- build rural schools
- encourage girl-child education
- improve teacher distribution
- modernize curriculum with digital literacy
2. Ending Rural–Urban Inequality
The development gap fuels crime. Solutions:
- balanced national budgets
- special rural development fund
- equal infrastructure priority
3. Building a Culture of Rule of Law
Citizens must believe:
- crime is punished
- justice is fair
- government is accountable
- corruption is minimized
This restores national confidence.
XIII. Key Metrics to Measure Success
A national strategy must track:
- reduction in kidnapping incidents
- decrease in ransom payments
- collapse of bandit logistics networks
- reclaimed forests
- increase in rural police response time
- economic growth in hotspots
- school attendance return rates
- community satisfaction surveys
- successful prosecution of masterminds
XIV. Final Framework: A 5-Year Strategic Roadmap
Year 1–2: Stabilization
- Air-ground dominance
- Forest doctrine implementation
- Unified command establishment
- Hotspot reclamation
- Border tightening
Year 2–4: Consolidation
- Rural development projects
- economic hubs
- grazing reforms
- justice system overhaul
- illegal mining crackdown
Year 4–5: Transformation
- full community integration
- education expansion
- permanent governance presence
- long-term intelligence mapping
- inter-state peace frameworks
Conclusion: A Nation Can Defeat Banditry Only Through a Whole-of-Society Strategy
Banditry is not a simple problem—it is the result of years of weak institutions, neglected communities, flawed economic systems, and security gaps. Only a national doctrine, executed with discipline, transparency, intelligence, and community partnership, can end the crisis permanently.
A nation that implements this roadmap will gradually move from:
- fear → confidence
- chaos → stability
- ungoverned spaces → civil order
- criminal dominance → state authority
This is not a short-term campaign. It is a national transformation project.
Community Safety & Public Alerts
What the Media Must Never Reveal During Active Security Operations

During active military, counterterrorism, or law-enforcement operations, the role of the media becomes extremely sensitive. One wrong headline or an overly detailed report can jeopardize troops, compromise strategy, alert hostile actors, or sabotage national security objectives.
Here is a full, expanded, professional breakdown of the information that must never be published during ongoing operations.
1. Real-Time Troop Movements and Deployment Routes
Publishing live updates such as:
- “Troops moving toward XYZ axis”
- “Reinforcements just departed ABC base”
- Livestreams of convoys
- Drone footage showing formations or advance paths
…directly exposes the mission.
Terror groups actively monitor open-source information, including local news, social media, and even Facebook Live.
This can allow them to:
- Set ambushes
- Reposition fighters
- Lay IEDs
- Evacuate targets
Operational secrecy is life-saving.
2. Identification of Units, Commanders, or Special Forces
Revealing:
- Names of field commanders
- Units or battalions involved
- Number of personnel
- Special forces participation
…makes them targets for retaliation, hostage-taking, or assassination.
Elite units rely on anonymity; exposing them compromises not just the operation, but future missions.
3. Coordinates, Base Locations, or Staging Areas
Anything that gives away:
- GPS coordinates
- Images showing recognizable landmarks
- Maps of planned attack routes
- Drone stills revealing terrain features
…helps hostile actors triangulate positions and plan counterattacks.
Even a single photo with metadata can expose sensitive locations.
4. Weapons, Equipment, and Tactical Capability Details
Media should avoid showing:
- Exact weapons in use
- Armored vehicle types
- New technological tools
- UAV flight patterns
- Electronic warfare devices
Terror groups can use this to measure capability, prepare countermeasures, or exploit weaknesses.
5. Casualty Numbers During the Operation
Premature reports of:
- Soldiers killed or injured
- Equipment destroyed
- “Heavy losses reported”
…can crush troop morale, affect families, and give terrorists propaganda material.
Numbers should only be released after the operation concludes, through an authorized spokesperson.
6. Classified Communications or Leaked Audio
Airwave intercepts, distress calls, or command transmissions should never be leaked or shared.
Terror groups can decode patterns or gauge response times.
7. Civilian Tips, Informant Identities, or Community Cooperation
Revealing:
- Local informants
- Villagers who provided intel
- Pictures of community collaborators
…can lead to immediate reprisals, killings, or mass punishment by terror groups.
Protecting civilians is paramount.
8. Premature Victory Statements
Declaring:
- “Operation successful”
- “Terrorists neutralized”
- “Hostages rescued”
…while the operation is ongoing can cause:
- Hostile regrouping
- Escape attempts
- Panic reactions
- Attacks on another location
Terrorists read media in real time.
9. Images Showing Troop Weakness or Vulnerability
Photos revealing:
- Low ammunition
- Injured troops
- Overwhelmed checkpoints
- Poor logistics
…are immediately exploited as psychological warfare material.
10. Internal Disagreements or Blame Games
Publishing reports of:
- Inter-agency conflict
- Blame between commanders
- Political interference
…during active ops signals weakness, encouraging terrorist boldness.
This type of reporting should wait for post-operation reviews.
Conclusion
Responsible reporting during active operations is not censorship — it is national security.
Media houses, bloggers, open-source intelligence pages, and citizen journalists must follow these rules strictly, because:
- Lives depend on it.
- Operational success depends on it.
- National morale and stability depend on it.
Well-timed, accurate, security-aware journalism strengthens the nation; reckless reporting endangers it.
Community Safety & Public Alerts
How Fake Information Strengthens Terror Groups and Undermines National Security
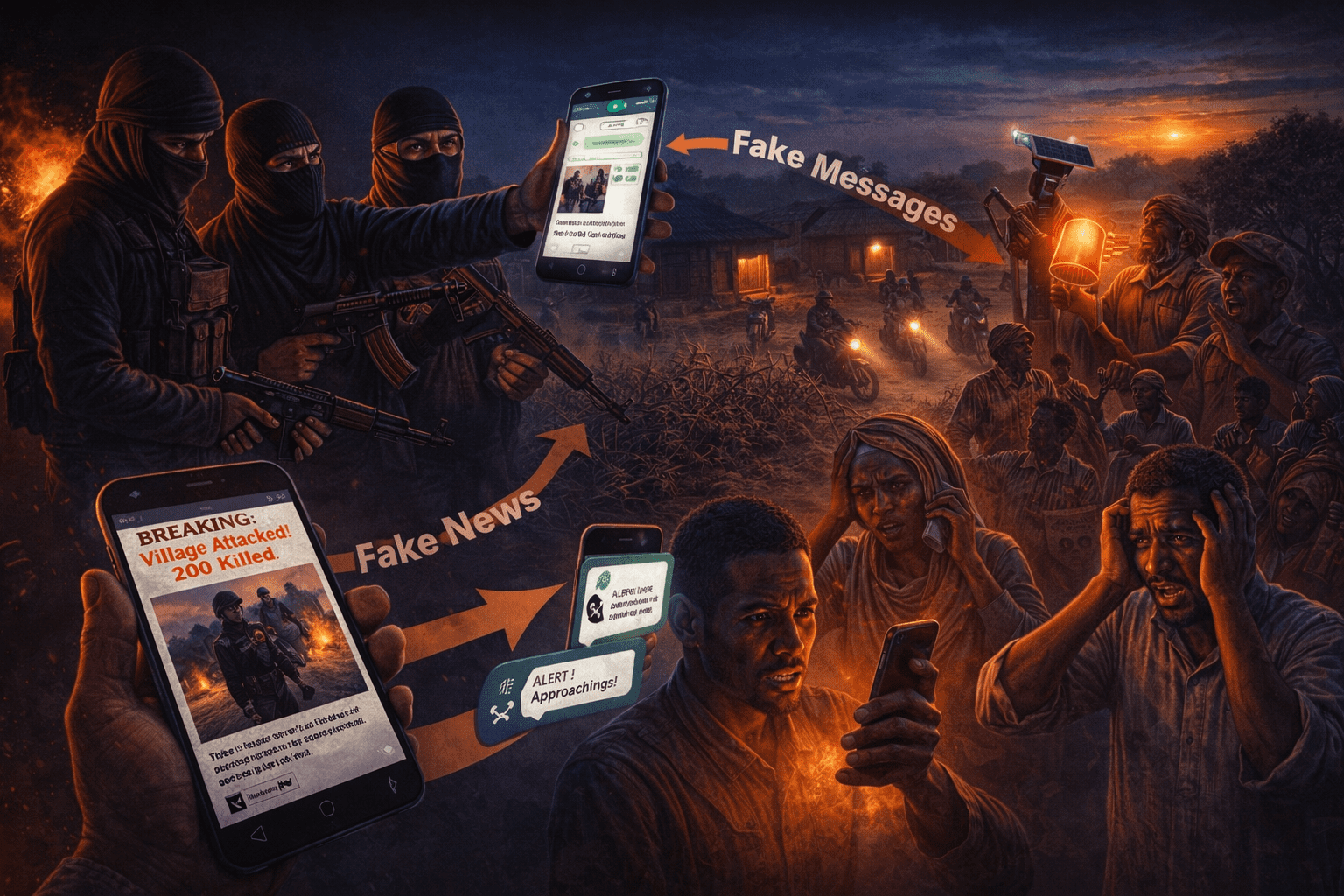
In modern conflict zones such as parts of Nigeria, misinformation has quietly become one of the most powerful weapons used by terror groups. Unlike guns and explosives, false information spreads faster, reaches more people, and can destabilise entire communities without a single shot fired. Understanding how fake information strengthens terror networks is essential for designing smarter counter-terrorism strategies.
1. Disinformation as a Psychological Weapon
Terror groups deliberately push false narratives to create fear, confusion, and emotional instability. When people don’t know what to believe, they panic more easily, overreact, or become distrustful of legitimate authorities.
Key tactics include:
• Exaggerating Their Strength
Groups claim they are “everywhere,” control multiple forests, or have thousands of fighters.
This inflates their perceived power and intimidates civilians.
• Creating Illusion of Supernatural Abilities
Fake stories like “they can disappear,” “they don’t die,” or “bullets don’t touch them” weaken community morale.
Terrorists thrive when people surrender mentally before any confrontation.
• Manufacturing Fake Warnings
Messages like “they will attack 20 villages tonight” force mass displacement, even where no threat exists.
This disrupts local economies and erodes citizens’ sense of security.
2. Manipulating Communities and Turning Them Against Each Other
Fake information often targets inter-community relationships:
• Inventing Ethnic or Religious Motives
Terrorists circulate audio notes claiming an ethnic group is “planning revenge,” pushing communities into suspicion and hostility.
• Spreading Fake Accusations
Rumours that innocent locals are informants or collaborators lead to wrongful targeting or internal conflict.
Result:
Communities become divided, distrust increases, and terrorists exploit the weakness.
3. Disinformation Weakens Security Agencies
Terror groups also use fake information to undermine national security efforts.
• Undermining Trust in Security Forces
Fake videos or voice notes claim soldiers “ran away,” “collected bribe,” or “abandoned villagers,” even when operations were successful.
Once people mistrust authorities, cooperation drops—and intelligence dries up.
• Flooding Channels with False Intel
Terrorists sometimes intentionally release too much fake tip-off information.
This:
- Wastes military logistics
- Distracts surveillance
- Forces troops to respond to fake alerts
It allows real attacks to succeed while forces are chasing shadows.
4. Disrupting Military Operations Through “Noise Warfare”
Fake information is also used tactically against operations.
• Announcing Fake Military Plans
Some groups spread audio claiming “troops will raid forest tonight.”
Residents panic and unintentionally pass this fake intel back to terrorists, who adjust their positions accordingly.
• Hiding Real Movement Behind Fake Messages
When many fake messages circulate, real warnings get ignored.
5. Recruitment Through Fake Propaganda
Terror groups use misinformation to lure members through:
• False Promises
They claim recruits will get money, safety, or religious rewards.
• Fake Success Stories
They showcase staged videos portraying luxury, unity, or strength, masking the harsh reality of exploitation and death.
• Manipulating Vulnerable Youth
Messages paint government forces as enemies and terrorists as protectors, shaping the minds of unemployed, uneducated, or isolated youths.
6. Creating Public Panic to Amplify Their Violence
A small attack becomes a massive fear event when amplified by fake information:
• Fake casualty numbers
Claiming 200 killed when only 5 died creates the illusion of overwhelming escalation.
• Staged videos of unrelated attacks
Old videos from other countries are shared as “new attacks.”
• Fake security breakdown stories
These create a narrative that terrorists are unstoppable.
The psychological impact sometimes causes more societal damage than the attack itself.
7. Why Fake Information Works So Well in Rural Areas
Many communities lack:
- Verified news sources
- Stable internet
- Digital literacy
- Psychological preparedness
Fake information spreads easily through:
- WhatsApp groups
- Market gossip
- Motorcyclists
- Audio notes
- Religious gatherings
- Town criers
When people can’t distinguish fact from fiction, terrorists get their strongest advantage.
8. How to Counter the Damage — Expert Recommendations
1. Build Trusted Local Information Channels
Community radio, verified WhatsApp broadcast lists, and church/mosque announcements can counter rumours.
2. Strengthen Digital Literacy
Teach villagers how to identify fake voice notes, edited videos, and recycled content.
3. Rapid Response Fact-Checking
Security agencies should quickly debunk fake threats before they spread.
4. Community Intelligence Cells
Select trusted community representatives who receive verified updates.
5. Stronger Civil-Military Relations
When soldiers regularly visit communities, people trust official information more than rumours.
6. Penalties for Deliberate Disinformation
Those intentionally spreading harmful fake intelligence must face legal sanctions.
Conclusion
Fake information is now as dangerous as bullets. Terror groups weaponise lies to manipulate emotions, weaken communities, mislead security agencies, and strengthen their operational advantage. Combating misinformation is therefore a critical component of national security—especially in fragile rural belts.
When communities learn to question information, verify sources, and trust credible channels, terrorists lose one of their most powerful invisible weapons.
-

 Community Safety & Public Alerts2 weeks ago
Community Safety & Public Alerts2 weeks ago2026 Security Outlook: Key Threat Trends Nigeria Must Prepare For
-

 Community Safety & Public Alerts2 weeks ago
Community Safety & Public Alerts2 weeks agoInside Nigeria’s Growing Border Security Challenge: How Weak Perimeters Fuel Crime Networks
-

 Community Safety & Public Alerts2 weeks ago
Community Safety & Public Alerts2 weeks agoHow Bandit Command Structures Operate Across Zamfara & Katsina: Inside the Criminal Networks
-

 Community Safety & Public Alerts2 weeks ago
Community Safety & Public Alerts2 weeks agoRising Kidnappings Across Nigeria: Security Agencies Intensify Crackdown as Criminal Networks Expand Their Operations
-

 Community Safety & Public Alerts2 weeks ago
Community Safety & Public Alerts2 weeks agoNigeria’s Border Security Crisis Deepens: How Porous Frontiers Fuel Arms Smuggling, Terror Mobility, and Rising Insecurity
-

 Community Safety & Public Alerts2 weeks ago
Community Safety & Public Alerts2 weeks agoRising Community Vigilance as Security Pressures Intensify Across Nigeria
-

 Terrorism & Insurgency1 week ago
Terrorism & Insurgency1 week agoWhy Troops Struggle in the Forest Belts of Niger State, Kaduna State and Katsina State
-

 Community Safety & Public Alerts2 weeks ago
Community Safety & Public Alerts2 weeks agoHow Technology Is quietly reshaping Rural Security Response in Nigeria